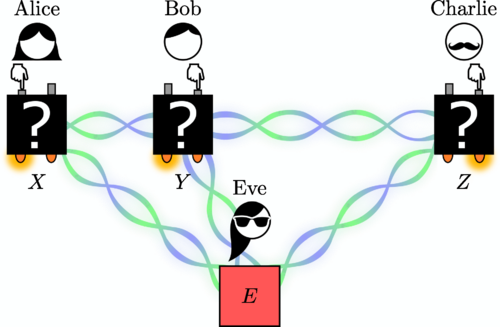
The authors quantify different uncertainties of eavesdropper Eve in a setting of multiparty device-independent cryptography. (c) Grasselli et al./PRX Quantum
ML4Q researchers led by Dagmar Bruss at HHU Düsseldorf have published recent results on multipartite device-independent (DI) protocols showing tight security proofs of DI conference key agreement and DI randomness generation protocols.
Congratulations to all the authors!
Publication
Entropy Bounds for Multiparty Device-Independent Cryptography
Federico Grasselli, Gláucia Murta, Hermann Kampermann, and Dagmar Bruß
PRX Quantum 2, 010308 – Published 14 January 2021
DOI: https://doi.org/10.1103/PRXQuantum.2.010308
Browse the ML4Q News Archive
Popular Summary
It is now widely accepted that the properties of quantum systems can be truly random while being highly correlated with the properties of other distant systems. Such correlations are said to be nonlocal, disproving our intuitive assumption that measuring a property of a system merely reveals a local pre-existing value. Remarkably, when nonlocality is observed in the outcomes of a set of parties measuring their quantum systems, one can infer that a party’s outcome is secret to some extent. Secret randomness is a crucial cryptographic primitive and nonlocality allows its certification regardless of the details of the physical implementation, namely in a device-independent manner. The challenge is to quantify the amount of secret randomness generated given the observed nonlocal correlations. Our paper provides the tools to certify the secret randomness generated by three or more parties (e.g., in a quantum network) when their measurement outcomes are nonlocally correlated.
The nonlocality of correlations is quantified by the violation of a given correlation inequality (Bell inequality), involving the outcomes of each collaborating party. We certify the fraction of secret bits in a single party’s outcome and in two parties’ outcomes by appropriate conditional entropies. In particular, we derive analytical expressions for the entropies that solely depend on the observed Bell violation. The derived conditional entropies play a fundamental role in the security proof of multiparty device-independent quantum-cryptographic protocols. Indeed, they determine the length of the bitstrings generated by randomness expansion and key agreement protocols.